[Avg. reading time: 5 minutes]
Communication Layer
MITM on MQTT / CoAP
Problem
MQTT and CoAP are lightweight protocols and are often deployed without strong encryption or authentication.
This makes them vulnerable to Man-in-the-Middle (MITM) attacks, where an attacker intercepts, reads, or alters traffic between the device and the broker/server.
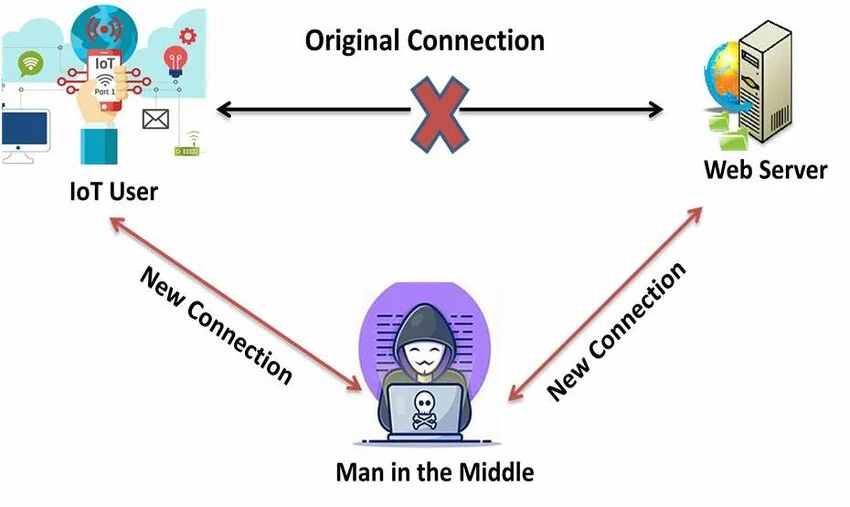
Example Scenario
A smart lighting system uses MQTT over plain TCP without TLS.
An attacker on the same network spoofs the broker and sends fake commands, causing all lights to turn off remotely.
Mitigation
- Use MQTT over TLS on port 8883
- Use CoAP over DTLS
- Enable mutual authentication using client and server certificates
- Verify broker/server identity before accepting a connection
- Use certificate pinning where appropriate
- Disable anonymous access on MQTT brokers
Replay Attacks Due to Lack of Freshness
Problem
Some IoT systems do not check whether a message is fresh.
If timestamps, nonces, or sequence numbers are missing, an attacker can capture a valid message and replay it later.
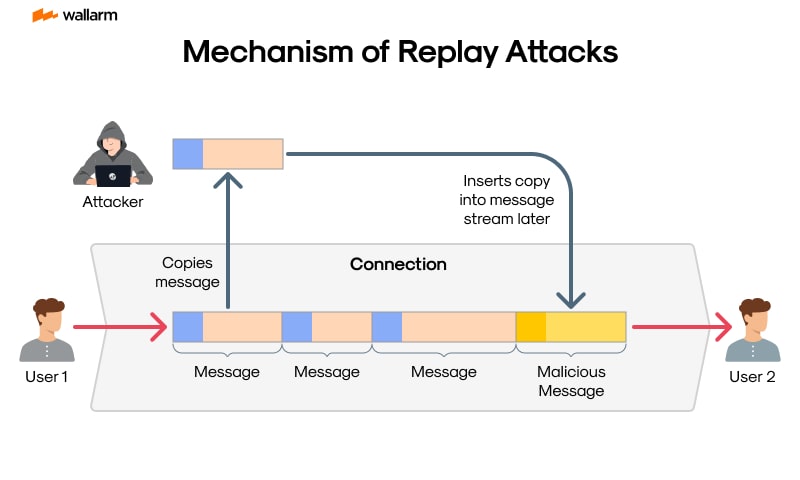
Example Scenario
A smart lock accepts an unlock command without checking whether the message is new.
An attacker records a valid unlock message and replays it later to gain unauthorized access.
Mitigation
- Add a timestamp, nonce, or message counter to each request
- Reject duplicate or expired messages
- Track recently used nonces or counters
- Use challenge-response for critical actions
- Use short-lived tokens with expiration checks
Example
{
"device_id": "lock01",
"command": "unlock",
"nonce": "839275abc123",
"timestamp": "2025-04-01T10:23:00Z"
}